| Hijacking Chromecast Is Easy |
| Written by Harry Fairhead | |||
| Wednesday, 23 July 2014 | |||
|
Chromecast, Google's streaming video USB stick, has a really clever way of allowing users to set it up. The trouble is that it might just be too clever. It turns out that what is easy for users to set up is also easy to hijack. When I first tried Chromecast I was impressed with it as an idea for making WiFi devices easier to setup. It seems unlikely that Google invented the idea, but it was the first time I had encountered it and I have to admit that I hadn't thought of it on my own. The idea is very simple. The big problem with setting up any WiFi-only device is that without a network connection you can't configure it and to get a network connection you have to configure it. It's a Catch 22 that the automatic configuration APIs and buttons were designed to solve but not all WiFi routers or access points provide this facility. Put simply, configuring a WiFi-only device isn't easy unless it has a full UI that can be used to enter the SSID and the password. What Google implemented, however, was very simple. When the Chromecast is first switched on, or doesn't have a WiFi connection, it first creates its own ad-hoc network with minimal security. This allows the Chromecast app running on a client device to connect to the ad-hoc network and communicate with the Chromecast. It then supplies the Chromecast with an SSID and password to allow it to connect to the proper, secured, WiFi network and everything from this point works as you would expect. You can see that the initial configuration isn't particularly secure in that any WiFi enabled device can connect to the Chromecast and configure it. The Chromecast does put a code up on the screen to make sure that you have the correct device, but the user isn't requested to enter it to take control, just to confirm that it is the correct device. This is the missed opportunity to secure the configuration stage.
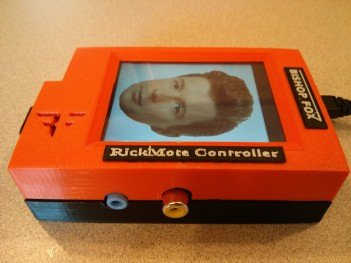
This is the loophole Dan Petro, a whitehat at Bishop Fox, has his Raspberry Pi-based device it takes over control of the Chromecast and makes it play Rick Astley’s well known song which has been used in the Rickroll joke for many years. If the owner of the Chromecast reconnects it the box simply re-hijacks the connection and continues playing the Rickcast. The way that it works is very simple. The Raspberry Pi sends a deauth command (de-authorize) which disconnects the Chromecast from the secure WiFi network and puts it back in ad-hoc mode. After that the Pi can connect to the device and take over. This video presentation shows how:
How serious is this hack? Given that the box doing the hacking has to be close enough for a WiFi connection to the Chromecast, it probably isn't as bad as someone taking over a baby alarm camera or a security camera. However, the potential for streaming undesirable videos to unsuspecting users is clear. The fix for the problem is also fairly simple, even if it hasn't been widely recognized. All Google has to do is patch the log-on procedure so that the Chromecast displays a short pin code on the TV screen and requires this to be input before any connection is made. The best that the Rickmote hack could do then is to knock the Chromecast off the network. What this means is that Google's method of connection the Chromecast using nothing but WiFi is still good - with one small change.
More InformationRelated ArticlesChromecast Creates Game Opportunities Bitcoin Isn't As Anonymous As You Might Hope Heartbleed - The Programmer's View MozDef - Mozilla's Self Defence Kit
To be informed about new articles on I Programmer, install the I Programmer Toolbar, subscribe to the RSS feed, follow us on, Twitter, Facebook, Google+ or Linkedin, or sign up for our weekly newsletter.
Comments
or email your comment to: comments@i-programmer.info |
|||
| Last Updated ( Wednesday, 23 July 2014 ) |