| Google Launches Free Vulnerability Scanner |
| Written by Sue Gee |
| Thursday, 29 December 2022 |
|
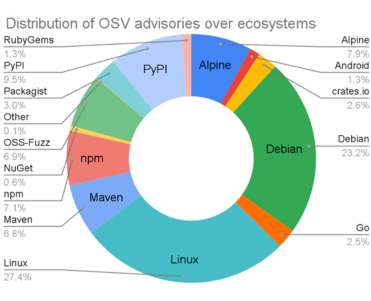
Google has announced the availability of OSV-Scanner, a free tool that acts as a front end interface to the Open Source Vulnerability (OSV) database. The OSV-Scanner assesses a project's dependencies against the OSV database showing all vulnerabilities relating to the project. As we reported at the time Google launched the OSV.dev service in 2021 as the first distributed open source vulnerability database. OSV allows all the different open source ecosystems and vulnerability databases to publish and consume information in one simple, precise, and machine readable format. As explained in Track Open Source Vulnerabilities With Google's OSV Database, OSV goes beyond beyond the current state of CVE tracking by using its own JSON schema for presenting vulnerability information which enables it to provide precise data on where a vulnerability was introduced and where it got fixed. Since its launch the OSV schema has been taken up by vulnerability databases such as GitHub Security Advisories and Android Security Bulletins. Altogether OSV.dev now supports 16 ecosystems, including all major language ecosystems, Linux distributions (Debian and Alpine), as well as Android, Linux Kernel, and OSS-Fuzz. This means the OSV.dev database is now the biggest open source vulnerability database of its kind, with a total of over 38,000 advisories.
According to Rex Pan of the Google Open Source Security Team: Since the OSV.dev database is open source and distributed, it has several benefits in comparison with closed source advisory databases and scanners:
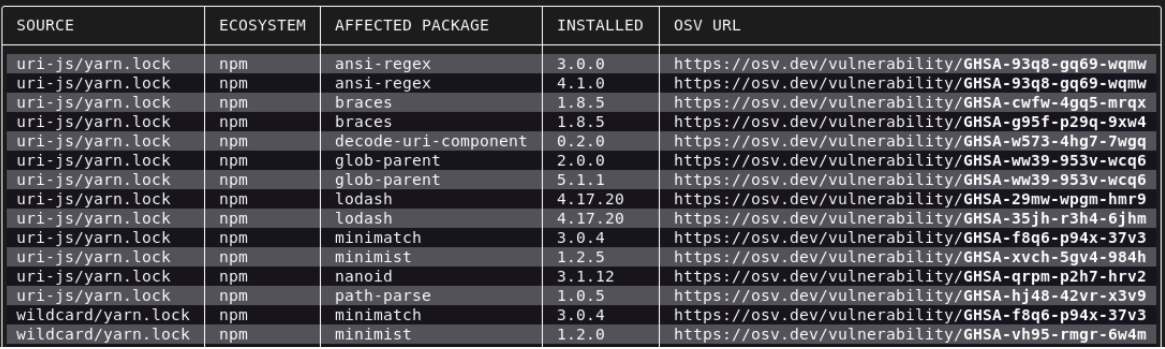
The OSV-Scanner is the next step and provides an officially supported frontend to the OSV database that connects a project’s list of dependencies with the vulnerabilities that affect them. The steps for installing and running the CLI on a project are on OSV's website. Running the scanner will first find all the transitive dependencies that are being used by analyzing manifests, SBOMs, and commit hashes. The scanner then connects this information with the OSV database and displays the vulnerabilities relevant to the project. More InformationAnnouncing OSV-Scanner: Vulnerability Scanner for Open Source Related ArticlesTrack Open Source Vulnerabilities With Google's OSV Database Secure Coding Best Practices for 2022 The State Of Secure Software Development - Three OpenSSF Courses Semgrep - More Than Just a Glorified Grep EU Bug Bounty - Software Security as a Civil Right To be informed about new articles on I Programmer, sign up for our weekly newsletter, subscribe to the RSS feed and follow us on Twitter, Facebook or Linkedin.
Comments
or email your comment to: comments@i-programmer.info |
| Last Updated ( Thursday, 29 December 2022 ) |