| Trust and Taint - University of Minnesota Banned By Linux |
| Monday, 26 April 2021 | |||
|
Greg Kroah-Hartman has banned the University of Minnesota from contributing to the Linux Kernel and gone to a great deal of effort to revert and re-evaluate 190 patches that had come from the same University. Is this an overreaction or is it the one and only possible response?
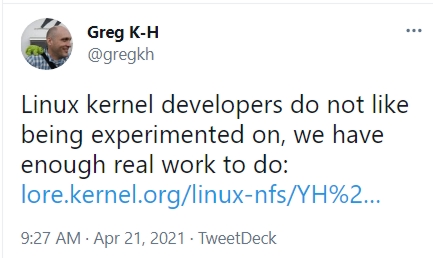
The irony of this situation is that the controversial project that led to loss of trust in the University of Minnesota was intended to improve the security of Linux. The research, conducted in August 2020, was by Kangije Lu, Assistant Professor and graduate student Qjushi Wu and their paper "On the Feasibility of Stealthily Introducing Vulnerabilities in Open-Source Software via Hypocrite Commits" has been accepted for 42nd IEEE Symposium on Security and Privacy. The research, which was supported by the NSF (National Science Foundation), included explicit safeguards to ensure that no bugs were merged into the Linux Kernel as a result of the experiment, although it now seems that a mutex close error many have slipped though, an error that has been fixed. The ban however wasn't made as a response to this paper. Instead the trigger was a more recent set of "obviously-incorrect patches" submitted by Aditya Pakki, another of Lu's Ph.D students who has explained that they were submitted as a result of his work on "a new static analyzer". For Kroah-Hartmann, who as the main Linux kernel maintainer, has the ultimate responsibility for its safety and security, the submission of new buggy patches was the last straw and his suspicion was that it again part of some research experiment as reflected in his tweet: The link in the tweet goes to an email reply to Aditya Pakki in which Hartmann writes: You, and your group, have publicly admitted to sending known-buggy patches to see how the kernel community would react to them, and published a paper based on that work. Now you submit a new series of obviously-incorrect patches again, so what am I supposed to think of such a thing? They obviously were _NOT_ created by a static analysis tool that is of any intelligence, as they all are the result of totally different patterns, and all of which are obviously not even fixing anything at all. So what am I supposed to think here, other than that you and your group are continuing to experiment on the kernel community developers by sending such nonsense patches?... Our community does not appreciate being experimented on, and being "tested" by submitting known patches that are either do nothing on purpose, or introduce bugs on purpose. If you wish to do work like this, I suggest you find a different community to run your experiments on, you are not welcome here. Because of this, I will now have to ban all future contributions from your University and rip out your previous contributions, as they were obviously submitted in bad-faith with the intent to cause problems. Asked his opinion Linus Torvalds, came up with a very mild response: "I don't think it has been a huge deal _technically_, but people are pissed off, and it's obviously a breach of trust." In an attempt to lift the ban, an apology was submitted yesterday as "An Open Letter to the Linux community and signed by Kangjie Lu, Qiushi Wu, and Aditya Pakki, University of Minnesota. It includes the statement: We just want you to know that we would never intentionally hurt the Linux kernel community and never introduce security vulnerabilities. Our work was conducted with the best of intentions and is all about finding and fixing security vulnerabilities. It later states: We are a research group whose members devote their careers to improving the Linux kernel. We have been working on finding and patching vulnerabilities in Linux for the past five years. The past observations with the patching process had motivated us to also study and address issues with the patching process itself. Acknowledging the anger felt towards them by the Linux community they say: We apologize unconditionally for what we now recognize was a breach of the shared trust in the open source community and seek forgiveness for our missteps. But it's not that simple. Trust was broken - and the action of this research group has tainted not just the three signatories to the open letter but the entire University of Minnesota. Hartman's response to this apology was a simple "Thank you" and refers to a letter sent by the Linux Foundation's Technical Advisory Board to the University of Miinesota outlining specific action required for the research group and the university in its entirety to regain the trust of the Linux kernel community. It seems entirely justified that it should take more than words to rebuild trust in this situation - but let's go further. This should never have been allowed to happen. Linux is mission-critical software relied on by big companies and even Mars exploration projects - it should not be seen as an environment in which do research, however laudable the aims of the research.
More InformationReply to "An Open Letter to the Linus Community" Related ArticlesGoogle Funding For Linux Security Taking Open Source Criticality Seriously Open Source Contributors - Payment and Other Motivation The Importance of Open Source Contributions What Attracts Devs To Open Source To be informed about new articles on I Programmer, sign up for our weekly newsletter, subscribe to the RSS feed and follow us on Twitter, Facebook or Linkedin.
Comments
or email your comment to: comments@i-programmer.info |
|||
| Last Updated ( Monday, 26 April 2021 ) |