| Visual Studio CTP 3 – With EF7 |
| Written by Kay Ewbank |
| Wednesday, 27 August 2014 |
|
Microsoft has released Community Technology Preview 3 of the next version of Visual Studio, along with an early build of the .NET Framework vNext, which brings with it an early version of Entity Framework 7. The new version includes improved tooling support for ASP.NET vNext, such as support for build configuration and support for unit tests. .NET Native has also been integrated into Visual Studio ‘14’. It includes initial support for calling WCF services within .NET Native apps and the associated Add Service Reference experience in Visual Studio.
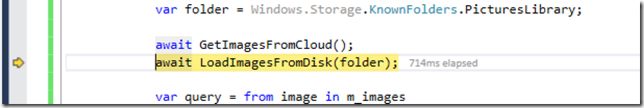
PerfTips are another area that has been improved. In CTP 3 you can see how long your code took to execute as you hit breakpoints and step through code with the debugger.
Visual C++ improvements are split into better adherence to the standard, and user productivity improvements. In the standards area, the compiler now supports the thread_local storage specifier, which allows objects to be stored separately for each thread. In the productivity area, Smart Tags (which used to show how to fix issues) have been replaced by Light Bulbs, which show up better and also offer a preview of the action before you take it. If you use Custom Layouts, which let you set up and save the layout of your tool window, they will now appear on any machine that has CTP 3 installed if you signed into the IDE with the same account. The other mainstream change worth mentioning is support for the creation of shared projects in C#, VB, and JavaScript. According to the blog post about the CTP: “Windows Store/Phone Projects written in C#/VB/JavaScript, as well as some classic desktop projects (Console Application, Class Library, Windows Form Application, Portable Class Library, WPF) written in C#/VB can consume one or many of these shared projects.” If you’re using the CTP with data, in addition to including Entity Framework 6.1.1 runtime, the new CTP also includes an early preview of ASP.NET vNext, which in turn includes a very early build of EF7. As with previous CTPs of Visual Studio “14”, this build of EF7 implements basic functionality and there are a number of limitations with the features that are implemented. The developers say that the preview is designed to give you an idea of what the experience will be like and you will quickly hit limitations if you deviate from the code from the default project template. CTP 3 can be downloaded from MSDN or from the Microsoft Download Center.
More InformationVisual Studio “14” CTP 3 ReleasedDownload Visual Studio "14" CTP Visual Studio "14" CTP Release Notes Related ArticlesTo be informed about new articles on I Programmer, install the I Programmer Toolbar, subscribe to the RSS feed, follow us on, Twitter, Facebook, Google+ or Linkedin, or sign up for our weekly newsletter.
Comments
or email your comment to: comments@i-programmer.info |
| Last Updated ( Wednesday, 27 August 2014 ) |