Programming News and Views
Send your programming press releases, news items or comments to: NewsDesk@i-programmer.info
Why Drone Shows Are Booming 04 Jul | Lucy Black  What do you need to make a celebration noteworthy? You may automatically think fireworks, especially for Independence Day, but an increasing number of celebrations are turning to drone shows instead. |
Mitch Kapor Gains MSc 45 Years After Dropping Out of MIT 04 Jul | Janet Swift 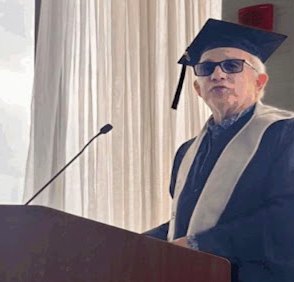 Mitch Kapor, founder of Lotus Development Corporation and designer of Lotus 1-2-3, the "killer application" which made the personal computer ubiquitous in the business world in the 1980s has completed his MSc from MIT's Sloan School of Management, started in 1979. |
Two Tools To Elevate Your MongoDB Experience 03 Jul | Nikos Vaggalis  The tools contradict each other; the first one allows you to write SQL instead of using Mongo's special syntax, while the other allows you to manipulate the database without having to write SQL and by just employing natural language. |
Mozilla Discontinues DeepSpeech 03 Jul | Kay Ewbank  The DeepSpeech project started by Mozilla has updated its GitHub page with the message "This project is now discontinued", and a change in the project status to archived. |
Computer Science Under Threat 02 Jul | Sue Gee  As the demand for "entry-level" programmers declines, established university Computer Science (CS) departments are facing a shortfall of students. How should they adapt their admission policies and what should high school students aspiring to a career in software development do to respond to the era of generative AI. |
CISA and NSA - Use Rust Or Perhaps Java 02 Jul | Mike James  The CISA and the NSA are urging us to adopt memory-safe languages (MSLs) for the sake of cybersecurity. You probably think they mean Rust but things aren't as clear cut as you might expect. |
Google Releases Python Client For Data Commons 01 Jul | Alex Denham  Google has released a new Python client library for Data Commons based on the V2 REST API. They say the new library enhances how data developers can make use of Data Commons. |
Deno Not Giving Up Over JavaScript Trademark 01 Jul | Ian Elliot  Deno has faced a setback in its attempt to get Oracle to relinquish the JavaScript Trademark. The US Patents Office Trademark Trial and Appeal Board (TTAB) dismissed Deno's fraud claim which is one the three strands of its case against Oracle. Deno's focus going forward is the other two - genericness and abandonment. |
Parasoft Adds AI Assistant To C/C++ Test 30 Jun | Harry Fairhead  Parasoft has updated its C/C++ Test software with an AI-powered documentation assistant, along with complete support for MISRA C:2025 and auto-suppression of equivalent violations. C/C++ Test can be used for static analysis and unit testing of C and C++ code. |
Rust 1.88 Adds Naked Function Support 30 Jun | Kay Ewbank  Rust 1.88 has been released with support for naked functions and for Let chains. In addtion, from now on, Cargo will automatically run garbage collection on the cache in its home directory. |
Breaking The Cipher Of Mary Queen Of Scots 29 Jun | Lucy Black  Researchers who break ciphers for fun have been talking about how they broke the coded letters of Mary Queen of Scots using a combination of computer algorithms, linguistic analysis and manual codebreaking techniques. |
June Week 4 28 Jun | Administrator  This week saw the publication of another title in the I Programmer Library published by I/O Press. It was prompted by the recent release of the Pico 2W, the WiFi version of the second generation Pico microcontroller from Raspberry Pi. You'll find details of the new book in BookWatch and we have an extract in which Harry Fairhead deals with a significant problem with the device. |
Apple's Swift Is Coming To Android 27 Jun | Mike James  Swift has long lost its position as a proprietary language, but what could Apple be thinking as it makes its move to the Android platform? |
MCP For Beginners Course 27 Jun | Editor  This course, provided by Microsoft, is based on a Github repository full of invaluable information that introduces MCP, Model Context Protocol, to beginners. |
Ktor 3.2 Adds HTMX Support 26 Jun | Mike James  Ktor 3.2 has been released with new modules for dependency injection and HTMX. This version also adds support for Gradle version catalogs. |
Jakarta EE 11 Modernises Test Kits 26 Jun | Kay Ewbank  The Eclipse Foundation has announced the general availability of the Jakarta EE 11 Platform. This release has modernised Test Compatibility Kits (TCKs), and introduces the Jakarta Data specification, along with major updates to the existing specifications. |
The Impact Of Code Club 25 Jun | Sue Gee  In the era of AI, the Raspberry Pi Foundation takes the view that learning how to create with technology has never been more important. Last year it revamped its Code Club network of free coding clubs with the aim of reaching 10 million young people over the next decade. |
The Future Of JavaScript - Stage 3 Propsals 25 Jun | Ian Elliot  The new proposals for ECMA Script/JavaScript have reached Stage 3, which means they will soon be with us. Is there room for excitement? |
Other Articles
|

Book Review
02 Jul
Author: Nick Morgan |
Featured Articles
Mitch Kapor and Lotus 1-2-3 04 Jul | Historian  The spreadsheet was a remarkable invention and yet the people who pioneered it didn't reap all the rewards they should have. Today we take spreadsheets for granted, but there is fascinating story lurking behind the scenes. |
The Trick Of The Mind - Regular Little Language 01 Jul | Mike James  Regular expressions are another example of a little language - expressive yes but not Turing complete. This is an extract from my book Trick of the Mind which explores what it is to be a programmer. |
Taxicab Geometry Problems 27 Jun | Joe Celko  In the conference season, developers face the perennial problem of getting from one hotel to another to meet colleagues. How good is your ability to write procedures to find shortest distance in a city block setting. Let's look at how the team at International Storm Door & Software set out the problem of Taxicab Geometry. |
The Pico/W In C: Erratum E9 Pull Down Problems 23 Jun | Harry Fairhead  There is an unfortunate problem with the new Pico 2 - its input stage has more leakage than you might expect and what is more this is non-linear and so leads to some strange behavior. This is an extract from my newly published book all about the Pico/W and Pico 2/W in C. |
Reverse Polish Notation - RPN 22 Jun | Harry Fairhead  RPN or Reverse Polish Notation used to be a basic of the computer programmer's world, but today it is not as well known. Hence there may be some perfectly clued up programmers who are still left wondering what the sausage is doing outside of the bun. |
Unhandled Exception!
|
Book Watch
Follow Book Watch on Twitter
Book Watch is I Programmer's listing of new books and is compiled using publishers' publicity material. It is not to be read as a review where we provide an independent assessment. Some but by no means all of the books in Book Watch are eventually reviewed.
04 Jul This book introduces the ways that artificial intelligence can make life as a coder easier. Chris Minnick explains the tools that can produce, examine, and fix code for you and looks at how to automate processes like code documentation, debugging, updating, and optimization. |
02 Jul Subtitled "A beginner's guide to building real-world, production-ready web apps with React 19 and TypeScript" in this book Carl Rippon shows the first steps in building modern-day component-based scalable web apps using the latest features and capabilities of React 19, TypeScript, and Next.js. Updated for React 19, this new edition covers new features such as React Server Components, server functions, and modern hooks, including useFormStatus and useActionState. The author shows building type-safe components using TypeScript. |
30 Jun This book provides the foundations for building software for the quantum age, and applying quantum computing to real-world business and research problems. Constantin Gonciulea and Charlee Stefanski lay out the math and programming techniques needed to apply quantum solutions to real challenges like sampling from classically intractable probability distributions and large-scale optimization problems. Developers will learn which quantum algorithms and patterns apply to different types of problems and how to build their first quantum applications. All the simulator code can be easily converted to run on real quantum hardware. |
More Book Watch
|
Previous Book Watch.
Follow Book Watch on Twitter.
Publishers send your book news to:
bookwatch@i-programmer.info